Outsourcing sensitive operations can accelerate growth, extend coverage, and improve efficiency. It can also introduce new layers of responsibility. When customer data, proprietary information, or regulated records leave your internal environment, leadership accountability does not disappear. That is why data security outsourcing requires deliberate evaluation before any contract is signed.
For U.S. SMEs and midmarket companies, the risk is rarely about intent. Most failures come from unclear expectations, weak controls, or assumptions that never made it into the agreement.
If you’re wondering how to evaluate data security when outsourcing services, the questions below are designed to help you assess readiness, maturity, and long-term fit before committing to a provider. Make sure to add these to your data protection outsourcing checklist.
What data will be accessed and why?
Security begins with precision. You should never outsource data without a shared understanding of scope.
In strong data security outsourcing engagements, both parties define exactly which data types are involved and which tasks require access. This includes customer identifiers, financial records, health information, internal dashboards, and system credentials.
Ask the provider to explain:
- What data categories are handled?
- Why is each category necessary for delivery?
- Which roles interact with each data type?
Clear scoping limits exposure and prevents privilege creep over time.
How is access granted, monitored, and removed?
Access control is where many outsourcing relationships weaken. Permissions that start small often expand quietly if not governed.
Mature data security outsourcing models rely on role-based access with formal approval workflows. Access should be traceable, reviewable, and reversible without delay.
Key questions include:
- How are access requests approved?
- Are access logs reviewed regularly?
- How fast is access removed during role changes or exits?
Strong controls protect both security and audit readiness.
How are internal security policies enforced daily?
Policies alone do not protect data. Behavior does.
A credible data security outsourcing partner should explain how written policies translate into everyday actions. This includes supervision, internal checks, and accountability at the team level.
Look for clarity around:
- How do supervisors enforce security protocols?
- What happens when policies are violated?
- How are corrective actions documented?
When it comes to outsourcing data protection, enforcement signals seriousness more than policy language ever will.
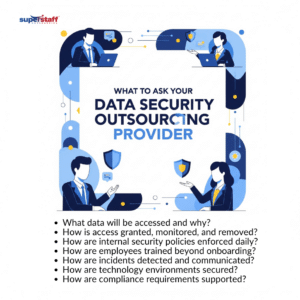
How are employees trained beyond onboarding?
Security awareness cannot stop after week one. Threats evolve, and habits drift.
Effective data security outsourcing programs invest in continuous education. Training should be practical, relevant, and reinforced over time.
Ask about:
- Frequency of refresher training
- Scenario-based learning tied to real workflows
- Validation methods such as assessments or audits
Ongoing training reduces human error and builds operational discipline.
How are incidents detected and communicated?
Even with strong controls, incidents can occur. The difference lies in response.
Reliable data security outsourcing partners define detection, escalation, and communication processes before anything goes wrong. Clients should never learn about issues late.
Important areas to clarify include:
- How are incidents identified?
- Who is notified and how quickly?
- What documentation is provided during and after resolution?
Prepared response frameworks protect trust when pressure is highest.
How are technology environments secured?
Security does not stop with people. Infrastructure matters just as much.
In disciplined data security outsourcing arrangements, providers control devices, networks, and systems tightly. This reduces reliance on individual judgment.
Ask how the provider manages:
- Company-issued devices versus personal equipment
- Network segmentation and access restrictions
- Data transfer limitations and monitoring
Infrastructure discipline supports consistent execution at scale.
How is data stored, backed up, and recovered?
Availability is part of security. Data that cannot be accessed when needed creates operational and reputational risk.
Strong data security outsourcing models include structured backup and recovery planning aligned with business priorities.
Clarify expectations around:
- Backup frequency and storage methods
- Recovery timelines after disruption
- Testing of recovery procedures
Resilience planning ensures continuity during unexpected events.
How are compliance requirements supported?
Outsourcing does not remove regulatory responsibility from your organization. It extends it.
A qualified data security outsourcing partner understands U.S. compliance expectations and adapts delivery accordingly. This includes healthcare, finance, retail, and technology environments.
Ask how the provider:
- Aligns internal controls with client regulations
- Supports audits and compliance reviews
- Adjusts processes as regulations change
Regulatory fluency reduces downstream risk and leadership exposure.
How is transparency maintained over time?
Security relationships should never be opaque. Visibility builds confidence.
Leading data security outsourcing partners provide regular updates, reviews, and reporting. This allows clients to govern proactively rather than reactively.
Useful transparency includes:
- Scheduled security reviews
- Incident summaries and trend analysis
- Advance notice of process changes
Ongoing visibility strengthens long-term partnership alignment.
How are responsibilities defined in the contract?
Contracts set expectations when stakes are highest. Vague language creates friction during critical moments.
Every data security outsourcing agreement should clearly define data ownership, breach responsibilities, escalation paths, and termination procedures.
Review whether the contract addresses:
- Data handling obligations
- Incident accountability
- Data return or destruction upon exit
Clarity in writing supports clarity in execution.
Why execution matters more than promises
Many providers describe similar security frameworks. What differentiates them is consistency.
In effective data security outsourcing relationships, security is embedded into daily operations rather than treated as a compliance checkbox. This shows up in supervision, reporting, and continuous improvement.
Execution quality determines whether controls hold under real-world pressure.
The Philippines as a secure outsourcing destination
The Philippines remains a preferred outsourcing destination for U.S. companies not only because of talent availability, but also because mature providers have built strong governance structures.
When managed correctly, data security outsourcing operations in the Philippines combine skilled professionals, structured controls, and close alignment with U.S. client expectations. Cultural compatibility and communication clarity further reduce operational risk.
The provider’s discipline matters more than geography alone.
Data Security Outsourcing with Confidence
Choosing an outsourcing partner is a strategic decision. It affects risk posture, brand trust, and operational resilience.
Before signing any agreement, leaders should ensure that data security outsourcing is addressed with precision, transparency, and accountability. The right questions surface readiness gaps early, when they are easiest to address.
At SuperStaff, data security outsourcing is treated as a shared responsibility. Our teams operate under strict access controls, continuous training, and clearly defined governance aligned with U.S. business requirements. We focus on execution, visibility, and long-term partnership, not surface-level assurances.
If you are evaluating outsourcing partners and want a security-first conversation grounded in real operational discipline, explore how SuperStaff can support your goals. Let us help you build an outsourcing model that protects your data while enabling sustainable growth.